Overcoming SBOM Workflow Complexities for Software Supply Chain Risk Management
As companies increasingly depend on open source software, defining and enforcing third party software policy compliance is critical to security, operational and legal risk management within your software supply chain. Software Bills of Materials (SBOMs) are essential in this context. An SBOM provides a detailed inventory of all software components in your codebase, helping organizations maintain software supply chain integrity. By clearly detailing each component with security vulnerability information and copyright and license information, a complete and accurate SBOM plays a vital role in reducing security risk and protecting intellectual property.
Here’s an overview for establishing effective SBOM workflows. By using these workflows, you can boost your company’s compliance efforts, protect intellectual property, and maintain a competitive advantage in the future.
Whether you’re new to the concept or seeking to improve your current processes, this guide will provide you with the necessary insights to confidently navigate the complexities of open source and third-party policy compliance.
Understanding the SBOM Ecosystem
Understanding the SBOM ecosystem is essential for securing your software supply chain. The visibility offered by a complete SBOM helps ensure each part of the software is documented and meets industry standards.
Nonetheless, creating and managing SBOMs presents its own challenges. In a complex software supply chain, tracking every component can be overwhelming. Third-party code can be introduced at the package manager, copy-pasted directly or generated by AI coding tools. Some third-party packages may be direct dependencies while others may be transient (dependencies of dependencies). All of these possibilities make accurate SBOM generation difficult. If not managed thoroughly, this complexity can result in legal and security gaps.
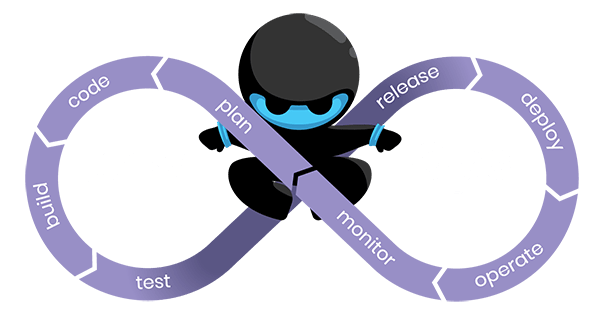
Building Effective SBOM Workflows
Creating a thorough SBOM workflow is essential for companies focused on safeguarding their software assets. Here’s how to begin:
- Identify All Software Components: Start by scanning and identifying every software component in use, including open source, commercial, and in some cases proprietary components too. This initial step takes stock of what you have; you need to confidently know your components before proceeding further.
- Trace Component Origins: With your codebase accurately scanned, investigate the origins of each component. Knowing the provenance of each component helps you prioritize potential vulnerabilities and intellectual property risks. Key data elements include CVEs, VEX data, and copyright and license – but consider the legislative, industry, customer or internal risk management requirements you are solving for.
- Automate the Process: Automation is necessary for this to be practical. Implement automated Sofware Composition Analysis (SCA) tools to streamline SBOM management, ensuring your inventory stays current without much manual input. Proper integration with your software development lifecycle will ensure your engineers’ productivity.
- Regularly Audit Your SBOM: As your software evolves, so should your SBOM. Incorporate updates into your regular development and code release processes to keep everything up-to-date, maintaining compliance and security over time.
By adhering to these steps, you can develop a successful SBOM workflow that ensures compliance, enhances security, and protects intellectual property. Consistency and automation are key – keeping your SBOM as dynamic as the software it documents.
Ensuring Accuracy and Auditability in SBOMs
Keeping your SBOMs up-to-date and auditable is vital for compliance and security throughout the software development lifecycle. Integrating updates into your CI/CD processes helps you document every change in your software components, allowing for continuous compliance without workflow disruption.
Automating the update process is an effective strategy. Using tools that automatically track and update your SBOMs can save time and minimize human error.
Resource allocation is often a concern when managing SBOMs. By leveraging automation and integrating updates into your development processes, you can handle this concern efficiently. Certainly, you should expect some level of manual review and validation that will require some domain expertise around software security and open source licenses. However, this expertise can be acquired by augmenting your staff with a partner, like FossID, that conducts open source audits and source code reviews.
Prioritizing these practices ensures that your SBOMs remain a reliable resource for compliance and security audits, ultimately safeguarding your company’s intellectual property and reputation.
Conclusion
Mastering SBOM workflows is essential for securing software and ensuring open source compliance. By creating a well-structured SBOM ecosystem, you protect intellectual property and encourage innovation. This process enables your organization to confidently manage the complexities of software development, reducing risks and enhancing security.
Proactively building and maintaining SBOM workflows is crucial. It helps you stay ahead of potential vulnerabilities and ensures software compliance with industry standards. An effective SBOM strategy goes beyond compliance, establishing a strong foundation for future growth and development.
In the dynamic automotive industry, a reliable SBOM process can distinguish your company. It shows a commitment to quality and security, significantly enhancing your brand’s reputation. As you progress, consider integrating these practices into your operations to drive success and maintain a competitive edge.
Frequently Asked Questions
Creating effective SBOM workflows can be overwhelming. What are the primary obstacles you might encounter?
Ensuring you have identified all dependencies, regardless of how well your code is managed and documented, is difficult. It requires tooling that can accurately scan your project using various techniques to catch all scenarios and an up-to-date open source software knowledge base. Monitoring each software component for changes in security vulnerabilities and license obligations is also challenging. Thirdly, watch out for process integration as you need to make sure your solution doesn’t hinder developer productivity or complicate release management.
How can you keep your SBOMs precise and current?
Employing automation with Software Composition Analysis (SCA) is beneficial in this context. Automated tools that detect all third-party components and monitor changes in software components are vital. Some level of human expertise should be expected to validate findings, annotate mitigating controls, or make nuanced corrections.
Regarding technologies that aid in efficient SBOM management, what should you look for?
Seek out those that provide robust detection methodologies and can integrate smoothly with your existing infrastructure. This helps keep your SBOMs consistently updated to reflect your software’s current status, simplifying compliance and security management.